Payment Gateway Decline Reasons Beyond Stripe

Payment gateway decline reasons are one of the least glamorous parts of running a subscription business, which is exactly why they end up draining so much revenue. Most SaaS teams see a failed payment in Stripe, glance at the decline code, and assume the problem starts and ends there. It doesn't. Stripe is often just the messenger. The real reason a payment failed can sit with the issuer, the card network, the customer’s bank, a fraud rule, a regulation like 3D Secure, stale card data, or a mismatch between how your billing flow works and how gateways evaluate risk.
If you want to reduce involuntary churn, you need to stop treating every decline as a generic failed charge and start sorting declines by what caused them, who controls the fix, and what action should happen next. That is the difference between retrying blindly and actually recovering revenue.
In this guide, we'll break down the most important payment gateway decline reasons beyond Stripe, show how to group them into useful operational buckets, and map each bucket to a concrete response. If you are already using Stripe, it also helps to compare these patterns against a broader decline code library so your team can separate temporary failures from structural ones faster.
Why decline reasons matter more than the raw failure count
A founder can look at a dashboard and see that 7% of recurring charges failed last month. That number is useful, but it is not actionable on its own. A failed payment caused by insufficient funds needs a different recovery playbook from a failed payment caused by authentication_required, invalid card details, or a hard issuer rejection. When those all get lumped together, teams make three expensive mistakes:
- they retry charges that should never be retried
- they stop retrying charges that were actually recoverable
- they blame the processor when the problem lives elsewhere
The core job is classification. A good decline taxonomy tells you whether the issue is:
- temporary and retryable
- customer-fixable
- merchant-fixable
- fraud or compliance related
- permanently unrecoverable
Once you have that, your dunning flow gets smarter overnight. Your emails improve. Your retry schedule gets tighter. Your support team stops improvising. Your product team sees where billing UX is making things worse.
The five layers where a recurring payment can fail
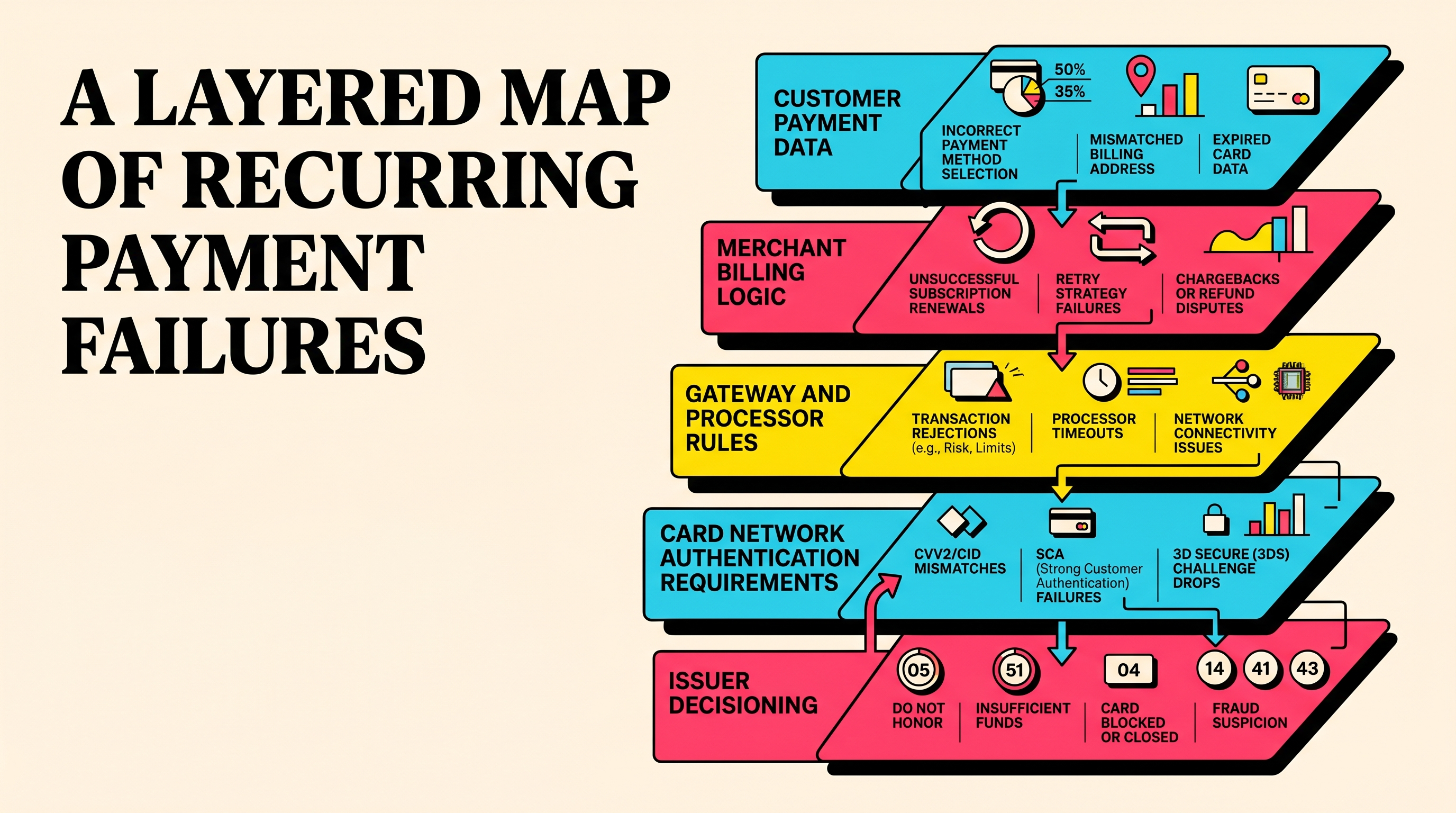
Most teams over-focus on the gateway because that is the system they can see. In reality, a recurring charge passes through a stack. A failure at any layer can bubble up as a decline.
1. Customer payment data
Bad card numbers, expired cards, outdated billing addresses, invalid CVC values, or cards that were replaced after fraud all start here. This is the most obvious category, but it is also the one many SaaS teams under-serve. If your update flow is clunky, buried, or scary-looking, customers delay fixing the issue.
2. Merchant setup and billing logic
Sometimes the payment method is fine, but your own billing setup creates avoidable declines. Common examples include charging at odd hours, retrying too aggressively, using the wrong payment descriptors, failing to trigger mandate or authentication flows correctly, or sending invoices with too little context. This is the category where “the gateway is broken” is often just cover for “our billing system is sloppy.”
3. Gateway and processor rules
Gateways route, tokenize, screen, and score transactions. They may reject a payment because risk checks fired, the payment method is unsupported for that transaction type, the merchant configuration is incomplete, or the charge violates local processing rules. Stripe exposes many of these outcomes, but similar patterns appear across Adyen, Braintree, Worldpay, Checkout.com, and other processors.
4. Card network and authentication requirements
Visa and Mastercard rules, issuer authentication flows, regional compliance requirements, and 3D Secure challenges can all interrupt recurring payments. A subscription charge may fail because authentication is required and the merchant did not bring the customer back into session, not because the customer lacks funds.
5. Issuer decisioning
This is the black box that drives founders nuts. The customer’s bank can decline for insufficient funds, suspected fraud, card restrictions, velocity limits, geographic mismatches, or reasons too vague to be useful. The issuer often has the final say. That means your recovery strategy has to be built around probability, not certainty.
A practical taxonomy of payment gateway decline reasons
The best framework is not technical purity. It is usefulness. Here is the one that tends to work for subscription businesses.
Soft declines: temporary failures that deserve another shot
Soft declines are the closest thing to easy money in involuntary churn work. These failures are often transient. The card may be valid. The customer may still want the product. The issue may clear on its own within hours or days.
Typical examples include:
- insufficient funds
- issuer unavailable
- do not honor in low-risk contexts
- processing error
- generic decline with prior successful history
- temporary network timeout or retry later responses
A soft decline should trigger three things immediately.
First, a controlled retry schedule. Not ten retries sprayed randomly across a week. A structured schedule based on your customer geography, pay cycles, and prior recovery performance. Second, customer messaging that is calm and specific. Third, segmentation. A long-tenured customer with a healthy payment history deserves a different retry posture from a brand new sign-up that failed on the first renewal.
This is also where benchmarks matter. If your soft-decline recovery rate is weak, the problem may not be your approval rate at all. It may be your retry design. Comparing your results against broader SaaS churn benchmarks helps you spot whether the leak is operational or structural.
What to do
- retry at times that match customer cash-flow patterns
- avoid stacking multiple retries in a narrow window
- use dunning emails that explain the issue without sounding accusatory
- suppress unnecessary support escalation on the first failure
- measure recovery rate by decline family, not just overall recovery rate
Hard declines: stop retrying and ask for a new payment method
Hard declines are where a lot of churn systems waste time. If a card is stolen, lost, closed, invalid, or explicitly unsupported, repeated retries will not magically fix it. They just create noise, risk, and customer irritation.
Common hard-decline examples include:
- lost card
- stolen card
- pickup card
- invalid number
- invalid account
- card account closed
- restricted card
- transaction not allowed
These declines call for a fast pivot. Your job is not to squeeze more retries out of the same card. Your job is to make updating the payment method almost frictionless.
What to do
- stop automated retries after the first confirmed hard decline
- send the customer directly to a secure payment update flow
- make the CTA obvious: update card, not “review billing details”
- keep support copy short and reassuring
- flag accounts so CSMs or support do not promise the retry system will fix it
A lot of involuntary churn hides in teams using the same workflow for hard and soft declines. That is self-inflicted damage.
Authentication and compliance declines: the SaaS tax nobody can ignore
This category has grown in importance as payment regulation has tightened. Declines like authentication_required, approval_with_id, or issuer responses tied to step-up verification are not really about card quality. They are about proving the transaction should be allowed.
For European subscriptions especially, this matters a lot. A card may be perfectly funded and still fail because strong customer authentication rules kicked in, the exemption logic was weak, or the off-session renewal did not have the right setup from the original mandate.
What to do
- ensure the first transaction is set up correctly for future off-session renewals
- bring customers back on-session when authentication is required
- explain that the payment was blocked for verification, not because the account is delinquent
- separate these declines from insufficient funds in reporting
- review recovery by market, because regional rules differ
If you lump authentication failures into a generic failed payment bucket, you miss the operational fix. These are product and billing-flow problems as much as they are payment problems.
Fraud and risk declines: sometimes the right recovery move is no recovery
Not every failed payment should be recovered. Some declines are signals to back off. Fraudulent, merchant blacklist, security violation, velocity exceeded, and similar codes are warnings that your risk posture matters more than short-term recovered MRR.
This is where founders get tempted to optimize the wrong metric. A system that forces more suspicious payments through can look good in the short run and ugly in dispute rates a month later.
What to do
- isolate suspected fraud declines from the standard dunning journey
- do not send aggressive retry emails for clearly suspicious activity
- review whether your fraud tooling is overly sensitive for renewals
- check whether legitimate long-time customers are being caught by changed risk rules
- coordinate risk, finance, and support instead of letting billing own the problem alone
The question here is not “How do we recover every dollar?” It is “Which dollars are safe and worth recovering?” That is a more adult metric.
Merchant-fixable declines: the painful category because it is your fault
These are the declines nobody enjoys diagnosing because the fix usually involves process, configuration, or UX work inside your own business.
Examples include:
- unsupported payment method for the billing flow you designed
- malformed request data
- duplicate transaction patterns
- poor statement descriptors that trigger customer confusion
- retry cadence that looks suspicious to issuers
- invoice timing that hits weekends or local holidays badly
- missing customer communication before a large annual renewal
This category is where operators win. A few boring improvements can outperform a fancy AI retry engine.
What to do
- audit recurring billing logic and retry spacing quarterly
- review issuer feedback and support tickets together
- test payment update flows on mobile, because that is where many customers open billing emails
- clean up billing descriptors so customers recognize the charge
- align renewal reminders with larger plan sizes and annual contracts
If you fix even two or three merchant-driven issues, your overall decline rate can drop without changing processor or sending more emails.
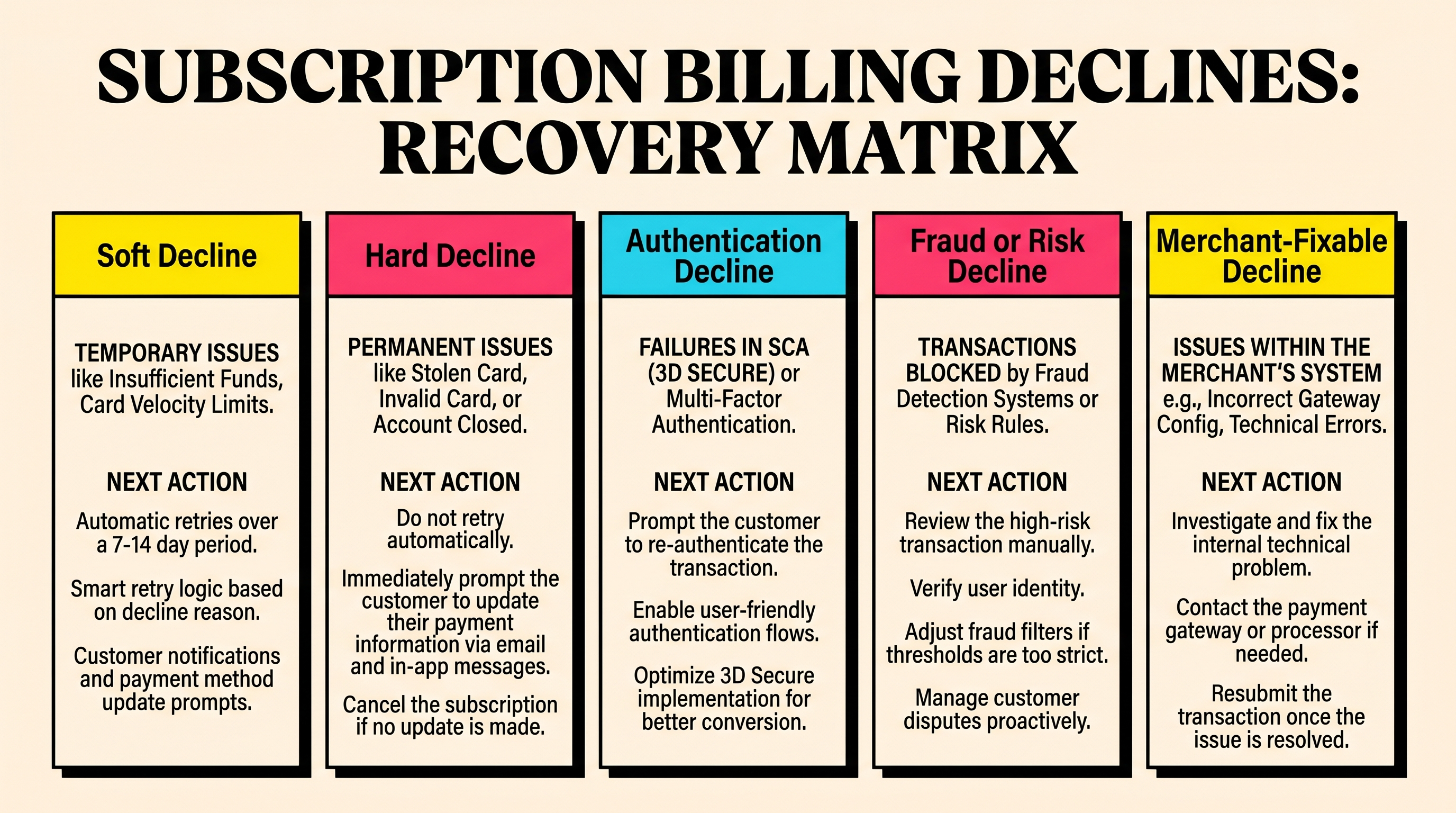
The recovery matrix every SaaS team should use
Not every decline needs a bespoke workflow, but every decline family needs an owner and a next step. A simple operating matrix works well:
Soft decline
- Owner: billing or revenue ops
- Action: retry on schedule, send light dunning, monitor recovery
Hard decline
- Owner: customer plus billing UX
- Action: request a new payment method immediately
Authentication decline
- Owner: product and billing engineering
- Action: return customer on-session and re-authenticate
Fraud or risk decline
- Owner: risk and finance
- Action: review, suppress standard recovery until safe
Merchant-fixable decline
- Owner: finance ops and engineering
- Action: correct workflow, configuration, or customer communication
This sounds simple because it is. The point is not complexity. The point is stopping a failed payment from becoming a vague problem nobody owns.
Metrics that actually help you improve decline performance
If you only track failed payments as a percentage of attempted renewals, you will miss the plot. Better metrics include:
- soft decline recovery rate within 7 days
- hard decline rate as a share of total failures
- authentication failure rate by region
- payment method update completion rate
- time to first customer notification
- revenue recovered per decline family
- avoidable decline rate caused by merchant configuration issues
The most useful cut is usually by decline family and customer segment. For example, if enterprise annual renewals are failing because authentication breaks on high-ticket invoices, that deserves a different fix from self-serve monthly plans with insufficient funds.
How to turn decline data into a better churn playbook
Most teams already have the raw data. They just do not operationalize it. Here is a clean way to do it.
Step 1: Normalize your decline reasons
Group gateway responses into the five categories above. Do not obsess over perfect granularity on day one. Get to usable buckets first.
Step 2: Attach a recommended action to each category
Every decline family should map to retry, update payment method, re-authenticate, manual review, or internal fix.
Step 3: Rewrite your customer messaging
A customer who needs to complete authentication should not get the same email as a customer with an expired card. Specificity lifts completion rates.
Step 4: Review your top decline families monthly
If one category is growing, investigate system changes, regional exposure, fraud rule changes, or billing cadence shifts.
Step 5: audit your Stripe account for hidden recovery gaps
Raw decline data is only half the story. The other half is whether your retry setup, payment method hygiene, and recovery workflow are leaving money on the table. That is exactly where a free audit is useful.
The blunt truth about payment gateway decline reasons
You do not need perfect issuer transparency to improve recovery. You need a better system for handling ambiguity. Payment gateway decline reasons beyond Stripe are messy, sometimes vague, and occasionally maddening. Fine. Build around that reality.
Separate soft from hard declines. Treat authentication failures as a flow problem, not just a payment problem. Stop retrying dead cards. Fix the merchant-side friction you control. Give each decline family a clear owner.
That alone will make your involuntary churn machine less dumb.
If you want to see where failed payments and recovery gaps are hiding in your billing setup, run a free churn audit at churnbot.co/audit.
Related Posts

7 Failed Payment Segments Every Stripe Team Should Track

9 Strategies to Stop Losing Customers to Payment Failures

Pre-Dunning: How to Prevent Failed Payments Before They Happen
How healthy is your Stripe account?
Get a free churn health report. Find pending cancellations, failed payments, and expiring cards putting your MRR at risk.
Run Free Audit